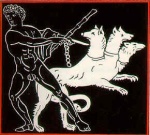
 Kerberos is a network authentication protocol which has been around for some time. Its based on asymmetric key cryptography and it best used for intra-organizational authentication tasks. Kerberos was developed by MIT and is distributed under a copyright permission notice very similar to the one used for the BSD operating and X11 Windowing system. Kerberos, by the way, is the name of the three-headed dog who guards the entrance to Hades.
Kerberos is a network authentication protocol which has been around for some time. Its based on asymmetric key cryptography and it best used for intra-organizational authentication tasks. Kerberos was developed by MIT and is distributed under a copyright permission notice very similar to the one used for the BSD operating and X11 Windowing system. Kerberos, by the way, is the name of the three-headed dog who guards the entrance to Hades.
Even if you're not interested in deploying Kerberos, understanding how it works is a good exercise if you're interested in secure authentication. You could read some dry technical document, but its more fun to read Designing an Authentication System: a Dialogue in Four Scenes, a short play about how Kerberos works. I don't know that its ever been performed, but its an entertaining read and will introduce you to the design issues and how they're solved in Kerberos. The issues are the same in any secure authentication system, and while the solutions might vary, knowing how Kerberos solved them is a good piece of knowledge to have in your toolbelt.




