Summary
Sovrin is an identity metasystem that provides the Internet's missing identity layer. By creating a general-purpose system for constructing context-specific identity systems, the metasystem represents a universal trust framework. A universal trust framework is the foundation for supporting life-like identity in our digital lives.

Imagine you are planning to meet a friend for lunch. You arrive at the restaurant on time and she’s nowhere to be found. You go to the hostess to inquire about the reservation. She tells you that your reservation is correct, and your friend is already there. She escorts you to the table where you greet your friend. You are seated and the hostess leaves you with a menu. Within a few moments, the waitress arrives to take your order. You ask a few questions about different dishes. You both settle on your order and the waitress leaves to communicate with the kitchen. You happily settle in to chat with your friend, while your food is being prepared.
In this scenario, you, your friend, the host, and waitstaff recognized, remembered, and interacted with people, places, and things countless times--that is “identity”. And this happened without anyone being aware that there was an identity system in play.
In the physical world, we effortlessly use identity to enable countless daily interactions. These interactions might be trivial or profound, temporary or permanent. We do this without any intervening administrator, without permission, without significant effort, and usually without much thought.
Identity just works--until you go online. Imagine this same scenario, helpfully curated by digital assistants.
You arrive at the restaurant after installing the FoodFinder app this restaurant uses to allow itself to be located. Of course, you have to create an account and log in. Once you find the place, you don’t see your friend, but then you recall you’re in the Alpha system and she’s Bravo, so you have to install the MeetWithFriends app that works in both. Once you open that app and log in, she is now visible, and you exchange greetings. After several minutes of explanation of the steps that she took to get to the table, you realize that you need to interact with what used to be the hostess station. It’s now a kiosk with a digital tablet. You attempt to sign in, but they’ve recently updated to HappyHostess from their previous system. Unfortunately, HappyHostess doesn’t have the data from the old system, so after you install the app, you are a new customer again and all your dining points have vanished. Oh well. The app gives you on screen directions to your table. After several wrong turns, due to unfamiliarity with the new app, you finally see your friend and can be seated. But you still can’t order or even talk to your friend at the table without logging into the restaurant’s LunchForYou app!
Unfortunately, we aren’t too far from this scenario now. In Alistair MacTaggart’s testimony before the Senate Commerce Committee in October, 2018, he described his experience at the local Super Cuts which required that he register with his email address and cell phone number at a kiosk in order to get a haircut. Frequent air travelers now encounter iPads at the restaurant tables in airports, so their order can go directly to the kitchen without human intervention. Unfortunately, it’s almost impossible to ask questions or have some special request. Your payment details go into the main system to correlate with whatever other information they have about you in order to “serve you better.”
Unfortunately, we are making identification in the offline world more like the complicated and messy digital world. Rather we should be building digital systems that mimic the natural and seamless interactions we have in the physical world.
The Problems with Digital Identity
Digital identity is broken because the Internet was built without an identity layer.
We say this so often it’s become cliché. The idea was made famous by a New Yorker cartoon that says, “On the Internet, nobody knows you’re a dog.”
But the reality is far from funny. The missing identity layer has resulted in a mishmash of one-off identity systems because every web site, service provider, and application has solved the problem in a unique way. As a result, people and organizations who use the Internet are subject to cognitive overload, friction, increased costs, loss of privacy, and even outright fraud.
Fixing the Internet’s identity problem is hard. There have been numerous systems, protocols, and standards proposed over the past 20 years. While most of them have provided improvements and fixed specific problems, none have offered a holistic solution.
To see why digital identity is so hard, let’s explore some specific problems that the online world presents that make identity different from the physical world1.
Proximity - Because we're not interacting with people physically, our traditional means of knowing who we're dealing with are useless. None of the familiar signals of the physical world are present. Consequently, it is difficult to reliably recognize and remember people and organizations online. Organizations have built so-called “administrative” identity systems to serve their own needs in recognizing and remembering their customers, but people don’t have the same capabilities. Consequently, we’re mired in myriad, incompatible systems built for narrow purposes.
Autonomy — Each of these administrative systems is built for the convenience of the organization who controls it. Design choices for these systems are made to maximize the legibility of people to the organization for its purposes. The balance of power is severely skewed toward one party over the other. Consequently, people have very few natural rights and little leverage online. Current online identity systems significatly reduce individual freedom and autonomy.
Privacy — No one will be surprised to learn that computers are very good at pattern matching. But a consequence of this is that online identity has very different implications for privacy than physical-world interactions. When you hand your driver’s license to the bartender to establish your legal age, you would be surprised if she could remember all the detailed information it contains, like your address, and do that for every patron she encountered. Computers, on the other hand retain a perfect memory of all the information they are presented with until they are told to forget.
Anonymity — Anonymity is closely related to privacy. In real life, we do without identity systems for most things. You don't have to identify yourself to the movie theater to watch a movie or log into some system to sit in a restaurant and have a private conversation with friends. Our interactions in the physical world are naturally anonymous. The ticket taker at a movie theater does “identify” you momentarily for purposes and checking your ticket, but that connection is ephemeral and thus anonymous for most purposes. Many online interactions could make use of ephemeral relationships as well in support of better privacy.
Flexibility — Closely related to the autonomy problem is one of flexibility. Current online identity systems are built for very narrow purposes. But real life is messy with billions of use cases. People are innovative and infinitely diverse. None of us presents the same picture of ourselves to everyone and everything—how we recognize, remember, and interact is highly dependent on the context.
Interoperability — A consequence of myriad identity silos is that we are unable to carry context from system to system. Your friend in one system might have a different identifier in another. The means you have for recognizing and remembering varies from system to system.
Scale — There are billions of people online. Each of them has dozens, even hundreds of relationships. The Internet of things promises to increase that by several orders of magnitude. Consequently, a general-purpose identity system needs to account for trillions of relationships between the many billions of people, organizations, and things that make up the online world.
An Identity Metasystem
Solving these problems requires building something more abstract and general than the one-off, context-specific identity systems of the past. The Internet is a monument to abstraction and generality. Rather than being a communications system like the telephone, the Internet is a communications metasystem. That is, the Internet is a system for building communications systems. Every new protocol changes the kinds of messages that the Internet can communicate and thus changes its nature.
Similarly, an identity layer for the Internet must be a metasystem that provides the building blocks and protocols necessary for others to build identity systems that meet the needs of any specific context or domain. An identity metasystem is a prerequisite for an online world where identity is as natural as it is in the physical world. An identity metasystem can remove the friction, decrease cognitive overload, and make online interactions more private and secure.
In 2005, Kim Cameron, Microsoft’s Chief Identity Architect, published the Laws of Identity (PDF), a paper that laid out seven important principles for how digital identity should work. In that paper, Kim describes an identity metasystem—a collection of interoperable identity systems—that can provide the missing identity layer:
...different identity systems must exist in a metasystem. It implies we need a simple encapsulating protocol (a way of agreeing on and transporting things). We also need a way to surface information through a unified user experience that allows individuals and organizations to select appropriate identity providers and features as they go about their daily activities. The universal identity metasystem must not be another monolith. It must be polycentric (federation implies this) and also polymorphic (existing in different forms). This will allow the identity ecology to emerge, evolve and self-organize.
From Kim’s description, we can identify several important features of an identity metasystem:
Encapsulating protocol—Protocols describe the rules for a set of interactions. An encapsulating protocol, then, describes the kinds of interactions that can happen without being overly prescriptive about the nature or content of those interactions. Thus, the encapsulating protocol enables a flexible set of interactions that can be adapted for specific contexts and needs. Protocols are the foundation of interoperability and allow for scale.
Unified user experience—Part of the beauty of natural identity systems is that we don’t have to switch apps or learn an entirely new way of interacting for each context. A unified user experience doesn’t mean a single user interface. Rather the focus is on the experience. As an example, consider an automobile. My grandfather, who died in 1955, could get in a modern car and, with only a little instruction, successfully drive it. Unified user experiences let people know what to expect and so they can intuitively understand how to interact in any given situation regardless of context.
User choice—By allowing people to select appropriate service providers and features, a metasystem allows for autonomy and flexibility. No single system can anticipate all the scenarios that come up as people live their lives. A metasystem allows for context-specific scenarios to be built and even supports ad hoc interactions that no one anticipated.
Modular—An identity metasystem can’t be a single, centralized system with limited pieces and parts. Rather, the metasystem will have interchangeable parts, built and operated by various parties. Protocols and standards enable this. Modularity supports substitutability, a key factor in autonomy and flexibility.
Polycentric—An identity metasystem is decentralized to enable autonomy and flexibility. No single system can anticipate all the various use cases. And no single actor should be allowed to determine who uses the system or for what purposes.
Polymorphic—The information we need to recognize, remember, and interact with various people, organizations, places, and things is context dependent and varies widely with the situation. The content that an identity metasystem carries must be flexible to support these.
The Laws of Identity
Kim follows this description of the metasystem with seven laws of identity that are designed to ensure that the metasystem is sufficiently respectful of autonomy, privacy, and security.
User Control and Consent—Technical identity systems must only reveal information identifying a user with the user’s consent.
Minimal Disclosure for a Constrained Use—The solution which discloses the least amount of identifying information and best limits its use is the most stable long-term solution.
Justifiable Parties—Digital identity systems must be designed so the disclosure of identifying information is limited to parties having a necessary and justifiable place in a given identity relationship.
Directed Identity—A universal identity system must support both “omni-directional” identifiers for use by public entities and “unidirectional” identifiers for use by private entities, thus facilitating discovery while preventing unnecessary release of correlation handles.
Pluralism of Operators and Technologies—A universal identity system must channel and enable the inter-working of multiple identity technologies run by multiple identity providers.
Human Integration—The universal identity metasystem must define the human user to be a component of the distributed system integrated through unambiguous human-machine communication mechanisms offering protection against identity attacks.
Consistent Experience Across Contexts—The unifying identity metasystem must guarantee its users a simple, consistent experience while enabling separation of contexts through multiple operators and technologies.
These laws describe outcomes without prescribing implementation. But they constrain architectural choices to ensure that the universal identity metasystem is not just usable, but also safe and secure.
Architecting a Universal Identity Metasystem
A universal identity metasystem must allow people to not only self-assert information but also bring to bear information that other parties know about them in any identity transaction.
The metasystem architecture has three primary features that allow it to be used as the basis for any context-specific identity system that is needed:
Relationships—the architecture must allow people, organizations, and things to have relationships with each other.
Messaging—the architecture must support messaging between the parties to those relationships.
Trustworthy Attribute Exchange—parties to relationships must be able to reliably exchange information about attributes (often called claims by identity professionals).
The architecture for the identity metasystem supplies these features using layers that build on each other as depicted in Figure 1.
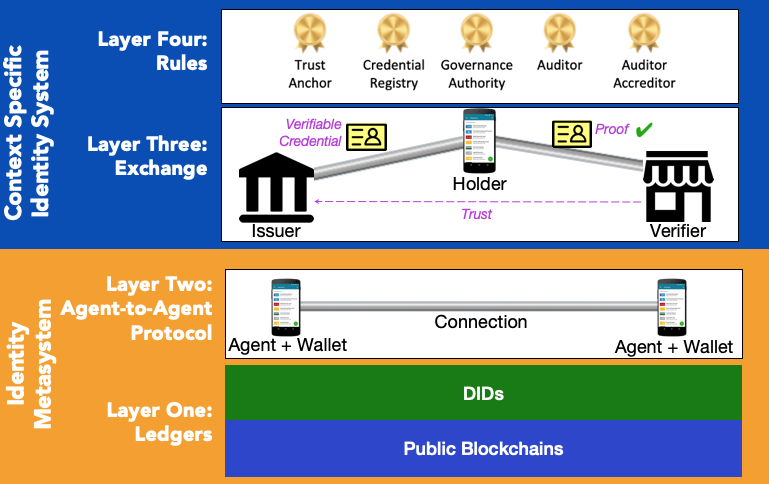
Relationships are created using a system of peer-to-peer agents in Layer 2. These agents exchange decentralized identifiers (DIDs) to create a relationship2. Because DIDs are cryptographic artifacts tied to public-private key pairs, this exchange provides the agents with the means to perform mutual authentication and create an encrypted channel. Agents use a messaging protocol called DIDComm to exchange messages.
DIDs exist in two forms, public and peer, which correspond to Cameron’s “omnidirectional” and “unidirectional” identifiers in the law on Directed Identity. Public DIDs can be universally resolved to reveal the public key and service endpoint of the owner. Peer DIDs are exchanged between parties to create relationships.
Agents exchange attributes over the channel created in Layer 2 using a flexible, decentralized system of credential exchange illustrated at Layer 3 in Figure 1. In credential exchange there are three parties: the credential issuer, the credential holder (sometimes called the identity owner), and the credential verifier (also known as the relying party).
A credential is a collection of claims (i.e. attributes) that is signed by the issuer and held by the identity owner. Credentials conform to the Verifiable Credential specification. While the word “credential” conjures images of formal documents, almost anything that can be represented in JSON can be attested using a credential. So, while things like passports and driver’s licenses fit this bill, so do things like membership cards, boarding passes, school report cards, invoices, purchase orders, and store receipts.
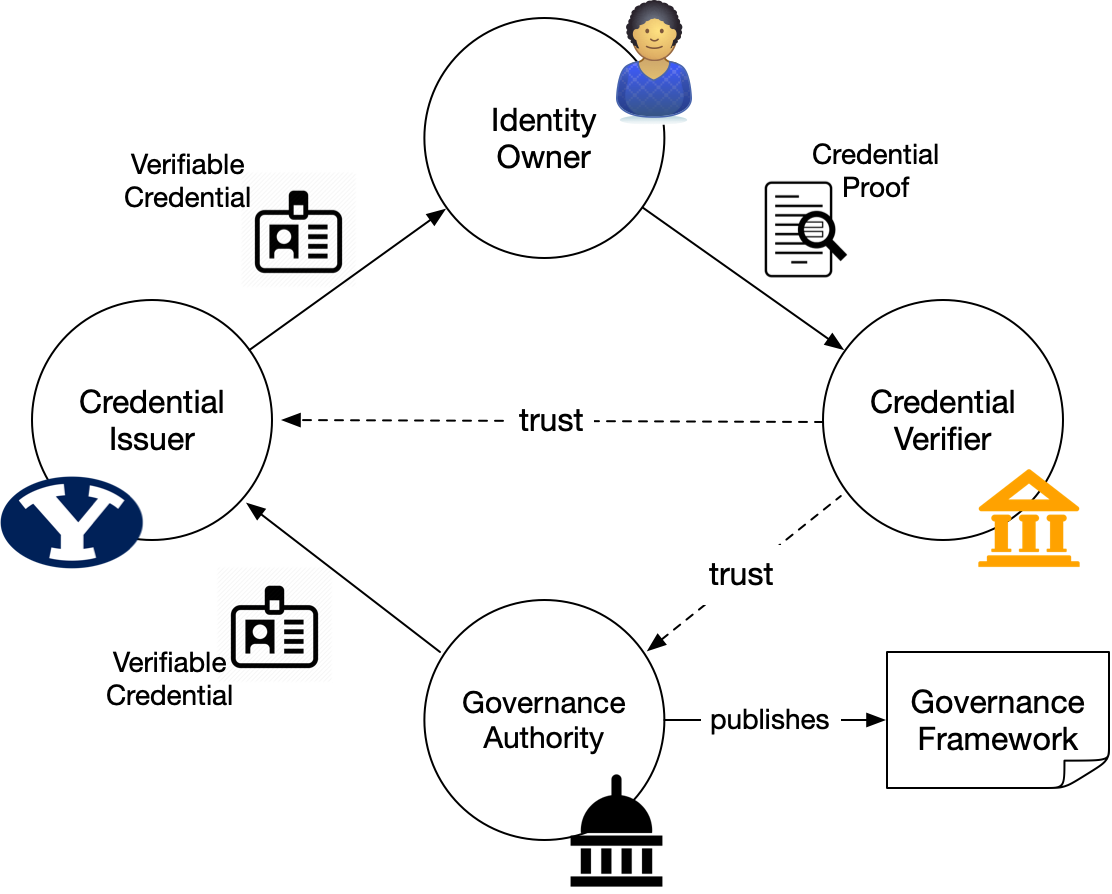
To see how credential exchange works, suppose Alice (the identity owner) is applying for a loan at her local bank (the credential verifier). The bank requires proof that Alice is employed and makes at least $70,000 per year. As shown in Figure 2, Alice’s employer (the credential issuer) has issued an employment credential that includes her employment status and her current salary. It might also include many other attributes related to Alice’s job. Alice holds the employment credential and can present it to prove to the bank that she is employed and makes more than $70,000.

When Alice proves her employment status to the bank, she doesn’t present the entire credential since doing so would reveal more information than is necessary. Instead, Alice presents just the information the bank needs using a cryptographic technique known as “zero knowledge proof.” The ability to limit the information presented from a credential is important to maintain privacy through the principle of minimal disclosure.
Trust and Accountability
For the identity metasystem to be useful, it has to trustworthy. Privacy can't come at the expense of accountability. For the metasystem to be trustworthy, Alice’s bank needs two levels of trust: first it needs to trust the mechanism of credential exchange provided by the metasystem. Specifically, the bank wants to know:
Who issued the credential,
That the credential was issued to Alice,
That the credential hasn’t been tampered with, and
That the credential hasn’t been revoked.
Trust in the metasystem is dependent on the ledger shown in Layer 1 in Figure 1. Alice’s bank can verify these four properties by looking at the credential definition on the ledger, retrieving the public DID and associated DID Document of the issuer from the ledger, and using the public key in the DID Document to check the signature of the credential to ensure it hasn’t been tampered with. The bank can also cryptographically verify that it was issued to Alice. As part of making her proof from the credential, Alice also proves that it has not been revoked by referencing the revocation registry, which is also available on the ledger. And, thanks to the ledger, the bank can do all of this without contacting the employer helping preserve Alice’s privacy.
The second level of trust depends on whether the bank can trust employer. The metasystem cannot supply this second level of trust. The bank wants to know that the identifier in the credential is associated with a legitimate business, the details of that business, and whether Alice really works there. The bank has several options for making these determinations depending on their internal policies. They could use an out of band method to validate the identifier of the issuer by, say, looking up the public DID of the issuer on their web site.
But in many cases, something more formal is required. This level of trust is provided by Layer 4 in Figure 1, context-specific governance and trust frameworks. Businesses, for example, are subject to regulation by the state they are located in. The regulatory framework for how businesses are registered constitutes the governance for a specific trust framework for legal businesses in that context. Figure 3 shows the credential flow from Figure 2 augmented with a governance framework.
Context-specific trust frameworks are numerous and varied. In most cases, they already exist because different domains have already established them for their own purposes. Defining credential schema and use cases, along with creating associated trust frameworks, is how identity systems are created on top of the identity metasystem.
A Universal Trust Framework
Relationships and interactions require trust. All new relationships have a "trust gap" that separates a place of certainty from something that is unknown. Some force has to help us "make the leap" from certainty to uncertainty and that force is trust3.
Traditionally, we've relied on local trust that is based on knowing someone—acquired knowledge or reputation. In a village, I know the participants and can rely on personal knowledge to determine who to trust. As society got larger, we began to rely on institutions to broker trust. Banks, for example, provide institutional trust by brokering transactions—we rely on the bank to transfer trust. For example, I don't need to trust you to take your credit card.
But institutional trust is problematic in the digital age. Trying to use ever-larger institutions to create trusted online interactions is what has gotten us into the current privacy mess, exemplified by security breaches and surveillance capitalism.
The identity metasystem represents a third way—a universal trust framework. A trust framework provides the structure necessary to overcome the trust gap and make the leap from the known to the unknown. Trust frameworks are all around us, but they are one-offs, too specialized to be universally applicable. For example, AirBnB is a trust framework, but the platform can only be used by AirBnB for trust transactions between hosts and guests. We can easily imagine AirBnB (or the next sharing platform) engineering their system to use the identity metasystem instead4.
The identity metasystem represents a universal trust framework because its trust model has five important characteristics:
Credentials are decentralized and contextual—There is no central authority for all credentials. Every party can be an issuer, a holder (identity owner), or a verifier. Verifiable credentials can be adapted to any country, any industry, any community, or any set of trust relationships.
Credential issuers decide on what data is contained in their credentials—Anyone can write credential schemas to the ledger. Anyone can create a credential definition based on any of these schemas.
Verifiers make their own trust decisions about which credentials to accept—There's no central authority who determines what credentials are important or which are used for what purpose. The metasystem supplies the technical underpinnings for cryptographic trust, upon which context-specific trust frameworks can operate.
Credential verifiers don't need to have any specific technical, contractual, or commercial relationship with credential issuers—Verifiers do not need to contact issuers to perform verification.
Credential holders are free to choose which credentials to carry and what information to disclose—People and organizations are in control of the credentials they hold (just as they are with physical credentials) and determine what to share with whom. This is sometimes referred to as self-sovereign identity (SSI).
These characteristics mirror how credentials work in the offline world. Rather than imagining a single identity or a single overarching institution—two models that represent the way digital identity has been done previously—the metasystem flexibly supports autonomy by allowing for as many interoperable trust frameworks as are needed to meet the myriad contexts in which humans find themselves.
Too much of our online (and physical world) interactions have come to rely on what Yuliya Panfil and Christopher Mellon call “monument credentials.” Monument credentials are the foundational documents upon which most of us build our formal identity, things like birth certificates, property titles, and passports. Monument credentials suffer from two primary challenges: access and accuracy.
An identity metasystem can provide an alternative to monument credentials in many situations. Panfil and Mellon call these “tapestry credentials.” Tapestry credentials are built from the data trails that we all leave as we navigate the digital world. these many credentials can provide a tapestry of new evidence that can be trusted for things we’ve relied on monument credentials for in the past. Taken together, they can be more accurate than a single monument credential. And because their based on many small interactions, they are more immediately available to many, especially under-documented populations.
Metasystems accelerate innovation and reduce engineering complexity by providing standard ways of doing things. Thus, universal solutions solve previously intractable problems and make new applications more broadly available. A trust framework with the characteristics listed above changes how we live our digital lives. The Internet changed the world because it provided a universal means of communicating. An identity metasystem changes the world by providing a universal means of trusting.
The real world is messy and unpredictable. Creating an identity system that is flexible enough to support the various ad hoc scenarios that the world presents us with can only be done using a general purpose metasystem. An automobile accident is one such complicated, real-life scenario. Dealing with an automobile accident entails multiple, independent credentials in a complex situation that involves a number of parties and plays out over several days or even weeks. I wrote about the power of an identity metasystem in these kinds of situations in an earlier post.
Solving the Problems
The identity metasystem solves the problems of digital identity discussed earlier. Let's see how:
Proximity—The metasystem solves the proximity problem through two primary mechanisms:
First, DIDs provide the means of reliably identifying the party you are interacting with and the cryptographic means to trust those relationships.
Second, credentials allow trusted third parties to attest to facts about the parties you interact with.
These enable trust to be built up over time and not be lost, the same way it is in the physical world.
Autonomy—Autonomy is at the heart of the metasystem’s architecture. Every party in credential exchange makes their own decisions. Every person and organization controls their relationships (i.e. private keys) and makes independent decisions about who to trust. Furthermore, the underlying protocols and standards allow for choice in tools and platforms.
Privacy—Privacy is the complement of autonomy: there is no privacy without autonomy and no autonomy without privacy. The metasystem incorporates privacy into its architecture through the support of peer DIDs, zero knowledge proofs, and many other features designed to protect people and organizations from unwanted correlations.
Anonymity—The metasystem allows people to retain their anonymity in online interactions. In many relationships, they can remain “nameless” by limiting the data that is disclosed. The metasystem removes the need for a centralized administrative system that can surveil activity. The metasystem also supports ephemeral relationships for short-lived interactions (e.g. with the ticket taker at the movie theater or bartender at the bar).
Flexibility—The metasystem can be used to construct identity systems for any purpose by designing a credential system to address the context-specific issues. The metasystem can be flexibly employed in ad hoc situations to bring credentials to bear from multiple contexts.
Interoperability—The underlying standards and protocols of the metasystem ensure that credential exchange is interoperable across contexts and between independent identity systems. The open-source nature of the reference code base for the metasystem ensures that multiple parties can bring interoperable solutions to market.
Scale—The metasystem scales for individuals through a consistent user experience which reduces cognitive load for people managing digital relationships. The peer-to-peer nature of the agent layer of the metasystem, combined with the widespread use of peer DIDs and decentralized nature of credential exchange, ensures that the metasystem can scale to support the trillions of relationships and credential exchanges necessary to provide an identity layer for the world’s economy.
While Obeying the Law
Simultaneously with solving the problems, the metasystem architecture must obey the laws of identity.
User Control and Consent—People are at the center of credential exchange and make independent choices about what relationships to create and what information to share.
Minimal Disclosure for a Constrained Use—The identity metasystem is designed to support minimal disclosure through zero-knowledge proof so that information is not shared unnecessarily.
Justifiable Parties—Only the credential issuer, holder, and verifier are part of any credential exchange. No third parties, intermediaries, or system administrators have access to the data in the credential or information about how it is shared.
Directed Identity—The metasystem uses public and peer DIDs to provide appropriate direction for identifiers.
Pluralism of Operators and Technologies—The flexibility of credential definitions, the layered architecture, open-source code base, and interoperable protocols make the metasystem flexible and open ensuring multiple solutions from many technology providers can be used.
Human Integration—The metasystem places the human in the loop for determining what relationships to create, how they are maintained, and what credentials to share with who.
Consistent Experience Across Contexts—The primary artifacts of the metasystem are relationships and credentials. Regardless of what specific design is used for the user interface, the experience is consistent because it rests on these artifacts.
Life-Like Digital Identity
We use identity in the physical world without thinking about it. And when we do, there are patterns that are so ingrained in our ways of interacting that we don’t give them a second thought. If we are to move more and more of our lives to the digital realm while also preserving agency and autonomy, we must create a digital world that allows us to jump the trust gap we inevitably have with people, organizations, and things when our interaction is digital.
An identity metasystem provides the long-missing identity layer for the Internet that will allow this to happen. The metasystem can be incorporated into every digital tool and system providing a consistent, trustworthy experience that feels as frictionless and natural as identity in the physical world.
Decentralized, self-sovereign identity depends on an identity metasystem and is the foundation for a decentralized Web—a Web that flexibly supports the kind of ad hoc interactions people have with each other all the time in real life. We'll never get an online world that mirrors real life and feels frictionless and life-like until we do.
Consequently, the arguments for creating the identity metasystem provided by the Sovrin Network are not narrow or technical issues. We are not building it simply for perceived technical benefits. Rather, the identity metasystem is vital for personal autonomy and ultimately human rights. Computers are coming to intermediate every aspect of our lives. Our autonomy and freedom as humans depend on how we architect this digital world. Unless we put digital systems under the control of the individuals they serve without intervening administrative authorities, the Internet will undermine the quality of life it's meant to bolster. The identity metasystem is the foundation for doing that.
End Notes
- I wrote about Fixing the Five Problems of Internet Identity in 2017. I've updated the list. Specifically, I think "autonomy" is a superset of "consent" and much more important overall.
- Decentralized identifiers are defined in specifications created by the W3C Decentralized Identifier Working Group. More details on decentralized identifiers and how they work can be found in Decentralized Identifiers.
- See We've Stopped Trusting Institutions and Started Trusting Strangers by Rachel Botsman
- I believe that a universal trust framework will lead to explosion of new sharing economy businesses because the identity metasystem will significantly reduce the plaform costs associated with building them.
Thanks to Joyce Searls, Doc Searls, and Drummond Reed for feedback on an earlier draft of this article.
Photo Credit: Friends Celebration Dinner Table from Pixabay (CC0)



