Summary
Avoiding future identity catastrophes requires that we put technical and legal structures in place now to protect privacy and autonomy and provide censorship resistance.
If you haven't yet seen Christopher Allen's excellent presentation on How to avoid another identity tragedy with SSI?, I encourage you to review the slides or watch the video of his recent presentation on SSIMeetup.org.
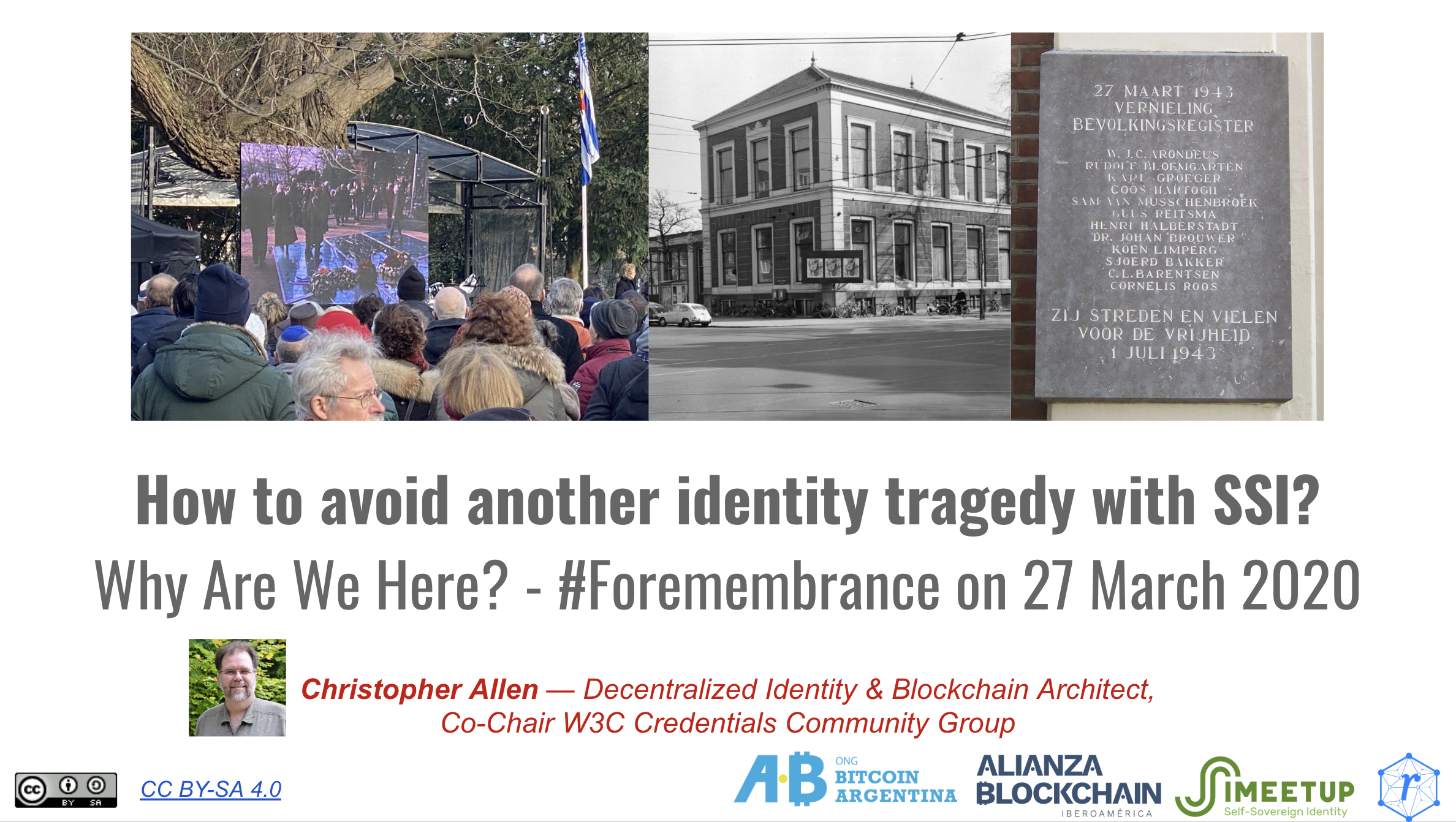
Christopher's point is simple: identity systems have real-world, sometimes life and death, consequences. Designers of identity systems must take care to ensure they're not unwittingly enabling some future identity dystopia. He uses the recent remembrance of Jews killed by Nazis in the Netherlands as an example of a well-intentioned identity system being used later by the Nazis to efficiently find and kill a larger percentage of the Jewish population there than elsewhere in Europe. The Neatherlands built the system in the 1930's as part of a civil registration project.
Christopher points to two major "tracks" in self-sovereign identity: LESS Identity and what Christopher terms "Trustless" (or "trust minimized") identity.
LESS Identity is a concept from Tim Bouma that is an acronym for "legally-enabled self-sovereign" identity. Tim defines the key characteristics of LESS Identity as:
- Minimum Disclosure: I want to disclose the absolute minimum to get a service or entitlement. If a service only needs to know I am legal to buy or receive something (because of age and/or residency) that's all they should get —not my name, date-of-birth, or my address.
- Full Control: I want full control over what I disclose. Not only at the point in time of the transaction, but all future uses that I may, or may not allow.
- Necessary Proofs: I understand that someone might not believe what I am providing — that’s ok — I should be able to provide proofs from the right authority—my age as proven by my local government, my academic degree as proven by my university.
- Legally-Enabled: All of the preceding requirements backed up by the necessary or applicable legal framework to protect me, and to protect those who are providing services to me (risk goes both ways in any transaction).
On the other hand, Christopher defines Trustless Identity as having the following characteristics:
- Anonymity
- Web of Trust
- Censorship Resistance
- Defend Human Rights against Powerful Actors (nation states, multi-national corps, mafias, etc.)
I've used the concepts of monument and tapestry credentials to talk about these different needs. Too many of our online (and physical world) interactions have come to rely on what Yuliya Panfil and Christopher Mellon call "monument credentials." Monument credentials are the foundational documents upon which most of us build our legal identity, things like birth certificates, property titles, and passports. This is the world of LESS Identity. But, for many, monument credentials suffer from two primary challenges: access and accuracy.
On the other hand, an identity metasystem can provide an alternative to monument credentials in many situations. Panfil and Mellon call these "tapestry credentials." Tapestry credentials are built from the data trails that we all leave as we navigate the digital world. These many credentials can provide a tapestry of evidence that can be trusted for things for which we’d otherwise rely on monument credentials. Taken together, they can be more accurate than a single monument credential. And because they're based on many small interactions, they are more immediately available to many, especially under-documented populations. Panfil and Mellon discuss, for example, how a system of tapestry credentials could be used in land administration.
More simply, think of things that you could prove through a credential-base web of trust where those whom you interact with day-to-day can say about you: things you've purchased, places you have been, flights you've taken, relationships you have, where you live, your family, where you work, and many other things can be attested by local organizations or the people you know. For many purposes, a tapestry of credentials can provide a sufficiently trustworthy foundation for achieving social goals.
A properly designed identity metasystem can balance the legitimate commercial and legal interests in credential exchange with the needs of everyone, in different contexts, for digital interactions that are privacy-preserving and autonomy-protecting. The Sovrin identity metasystem can provide for both LESS Identity (monument credentials) and Trustless Identity (tapestry credentials). There are several important characteristics of this identity metasystem that allow it to be useful in either context:
- Censorship Resistant—Censorship is broadly defined in an identity system as being able to keep someone from accessing and using the system for any reason. There are several features that increase resistance of the metasystem to censorship including removing intermediaries, anchoring credentials in a large, global pool of other credential definitions, and state proofs for easily verifying the integrity of a ledger lookup—even offline.
- Guardianship—There are many who won’t be in a position to manage their credentials directly for several reasons including not having access to the appropriate digital infrastructure, being too young, or otherwise lacking legal capacity (e.g. in a coma). We've spent considerable time on the legal and technical architectures necessary to support guardianship in Sovrin.
- Correlation Minimization—Our work on and support for the Peer DID Method Specification is one example of how we work to reduce correlation. Peer DIDs reduce correlation, increase privacy, and scale to trillions of connections. Peer DIDs are easy to rotate or cancel because each relationship uses a different identifier.
- Public DIDs for People—At the same time, people should be able to issue credentials to enable the wide use of tapestry credentials. GDPR, at present, limits the use of public DIDs for people (the root of an issued credential). Sovrin Foundation is engaged in discussions to balance data protection regulations with the legitimate needs of people to anchor credential definitions in a public ledger.
- Minimal Disclosure—Credential holders use the Sovrin identity metasystem to share information from credentials using zero-knowledge proofs The agent protocols include the infrastructure and tools to enable the process of communicating, negotiating, sending, and verifying the fidelity of zero knowledge proofs (ZKPs). This is a secure way to minimize the information that is disclosed in a credential exchange without limiting functionality or security.
Many people, focused on the needs of LESS Identity, have claimed these features are too costly and unnecessary. But Sovrin Network provides an existence proof that these are not only possible, but efficient and usable. There's no excuse to not implement these vital features, when the code for them is open and usable. Without these important features, we risk building an identity metasystem that meets the demands of LESS Identity, but runs the risk of a future catastrophe. By supporting these, the Sovrin Network shows that LESS Identity is not necessarily in conflict with the goals of Identity for All.
This support for both is vital. Support for LESS Identity is needed for wide adoption. Without that, a Trustless Identity system is worthless since it is immediately identifiable as "an other" and therefore easily censored. When both are running on the same infrastructure, would-be censors can't kill one without damaging the other. One of the biggest factors in resisting censorship is making censorship too costly.
Sovrin Foundation has been dedicated to the goal of Identity for All since its inception. This must include both monument and tapestry credential models supporting legally-enabled and trustless self-sovereign identity. Ensure Identity for All requires that we balance the needs of all stakeholders by ensuring the metasystem remains independent.




